Highlights:
- C5 is a government-backed verification framework implemented by the German Federal Office for Information Security (BSI).
- As more companies migrate their technologies to the cloud—especially after COVID—C5 helps determine which cloud providers meet the German government’s baseline security level.
- RingCentral is now compliant with C5:2020. Learn more about our security posture in our Trust Center.
From sophisticated vishing scams to Zoom bombings and DDOS attacks, security in the cloud is more important today than ever. After all, most businesses migrated a lot of their workflows to the cloud in the eve of the pandemic.
But this presents another question: how do you know which service providers—and their solutions—you can trust? Providers can tout multiple layers of security and an unwavering commitment to privacy, but that just makes evaluating providers much more difficult.
Everything you need to know about RingCentral security
At RingCentral, we understand that trust in our service isn’t given—it’s earned. That’s why we’re excited to announce that we’re now compliant with C5, Germany’s latest compliance standard.
Let’s look at what this means for RingCentral users.
What is C5?
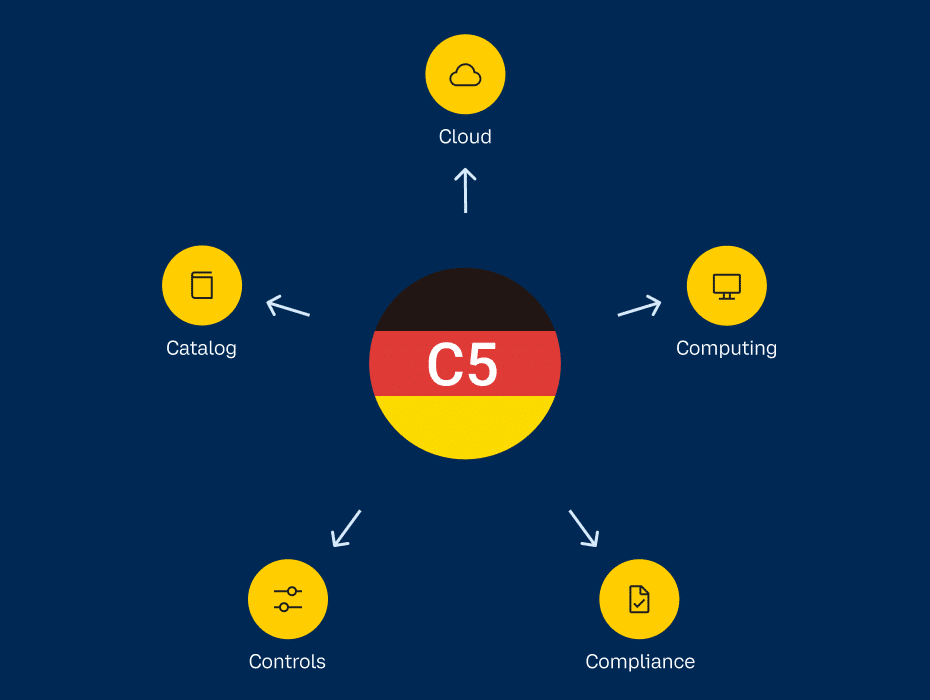
The C5 is a government-backed German verification framework implemented by the German Federal Office for Information Security (BSI). The five ‘C’s stand for Cloud, Computing, Compliance, Controls and Catalog (hence C5).
Introduced in 2016 and updated in 2020, in response to the ever-changing technology landscape, the BSI introduced the framework as a way to rigorously assess the levels of security of cloud services in the context of the German Government’s “Security Recommendations for Cloud Providers”.
Why does the C5 exist?
The overall objective of C5 is to increase the transparency of data protection in the cloud as organizations move away from traditional application and infrastructure responsibilities.
It helps cloud users know whether a cloud service provider has fulfilled their security requirements. These requirements can include:
- Securing the authorization and authentication of users to prevent unauthorized access
- Timeliness and reliability of access to and use of data
- Tracking of changes and transactions without adversely affecting their execution
- Safeguards to protect against malicious attacks
- Reviewing and managing operational workflow
Who is the C5 relevant for?
There are two sides to unpack here. First, C5 is a mandated requirement in Germany for those providing cloud services to government agencies. This applies to any service provider inside or outside of Germany.
How to find a cloud provider you can trust
Second, C5 acts as a framework for other countries to evaluate the security of cloud providers. Internationally-recognized standards are gaining steam especially for businesses that operate across borders.
In a nutshell, C5 benefits any organization looking for a belt-and-braces approach to its security standards that safeguards its business information and customer data. The verification is relevant for all parties, whether a cloud vendor, auditor, user, security provider or customer.
Our commitment to your security
There’s a lot to think about before moving your communications to the cloud—and security is a major piece of the puzzle. But you won’t have to go it alone.
Protecting your data is one of the highest priorities at RingCentral, and our compliance with C5:2020 from the BSI gives you the assurance that our solution meets stringent international security standards.
At the same time, RingCentral MVP also achieved three internationally recognised ISO certifications, including ISO 27001, ISO 27017 and ISO 27018 for information security best practices.
Our partnerships with European industry leaders such as Atos and Alcatel-Lucent Enterprise also demonstrate our commitment to protecting the data of our European user base. Adhering to European standards helps us meet local customer needs.
Always innovating on security
When you choose us as your communications provider, you trust that our security posture is always second to none. That’s why we continue to create new ways to guard your information.
Check out our latest announcement on Dynamic end-to-end encryption (E2EE) for RingCentral video meetings, along with how we built security into every part of RingCentral MVP.
You can also learn more about our overall security in our Trust Center.
Updated Dec 30, 2022