The CFTC’s notice to JPMorgan has just made the realm of real-time communications surveillance a billion-dollar topic for Board Rooms.
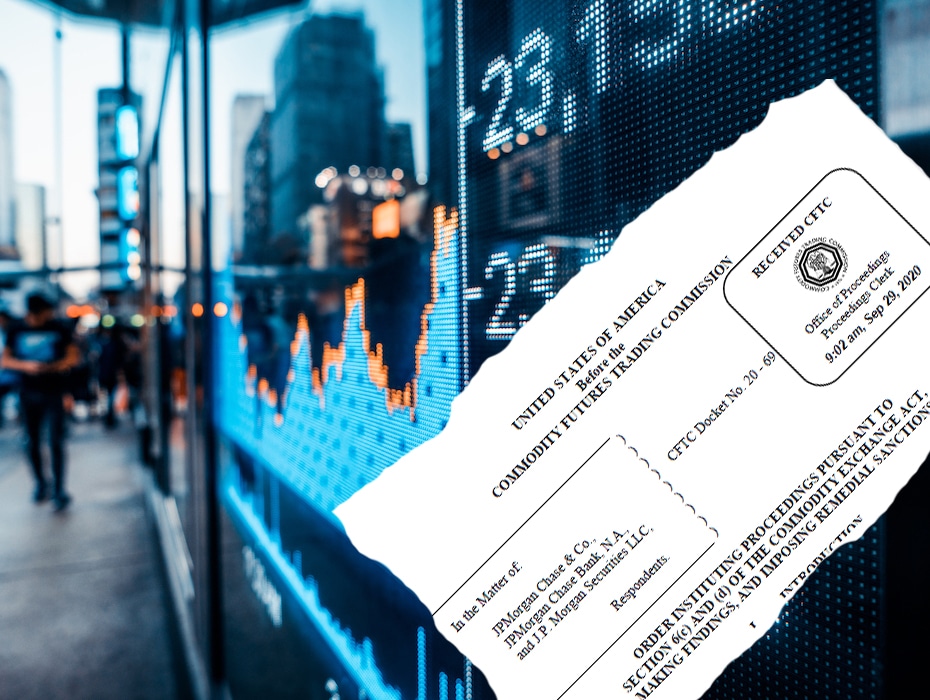
Last month, JPMorgan settled charges with the Commodity Futures Trading Commission (CFTC) for manipulative and deceptive trading conduct, specifically spoofing orders in precious metals and U.S. Treasury futures contracts. It was the largest fine ever imposed by the CFTC, nearly a billion dollars.
A harsh slap heard beyond the futures industry
“It’s an important message,” states CFTC Enforcement Director McDonald, who commits in its press release “to eradicate this unlawful activity and to hold those responsible fully accountable,” adding, “you will be caught, punished, and forced to give up your ill-gotten gains.”
Traders enter Spoof Orders to create a false impression of buying or selling interest, with the intent to manipulate market prices and trick market participants into trading based on their spoofing.
Regulated communications surveillance: an ineffective system
The CFTC Order reviews the actions that JP has taken and will take to enhance its market compliance program and internal controls. The usual actions are listed, such as updates to policies, supervisory actions, violation tracking, and increased resources and budget.
However, a critical part of the Order relates to building a more robust electronic communications surveillance program and capabilities. JPM attests to:
Increasing its electronic communications surveillance program, such that JPM’s communications surveillance platforms automatically ingest and process approximately 100 million messages on a monthly basis, and analysts review 100% of the alerts generated from these surveillances.
It appears that the messaging and voice, between the traders, fell outside of their risk surveillance systems. From reading the Order, this was an important issue in the CFTC’s determination that JPM’s surveillance system lacked the ability to effectively identify spoofing conduct.
In order to prove a violation of Regulation 166.3, the Commission must demonstrate the registrant’s supervisory system was generally inadequate or the registrant failed to perform its supervisory duties diligently.
Spoofing evidence: chat conversations
The CFTC presents a clear picture. Their spoofing evidence includes chat conversations, correlated with trade flow. The examples include Trader 1 chatting Trader 3 “just bid it up to . . . sell.” In another instance, chats to a Salesperson confirm another Trader is “bidding up on the futures trying to get some off… in case you were watching some large bids come into market.”
Firms have largely integrated real-time trading surveillance across order flow, asset classes, and trade venues. But the realm of real-time message, video, and voice surveillance has lots of room for improvement.
Real-time communications surveillance gaps
To detect spoofing, trading firms need to surveil much more than order flow and executions. This is the CFTC’s point:
Market participants have tackled fragmented venues and complex order types but not the fragmented and siloed communication methods.
Whereas firms have normalized, tagged, and aggregated trade data, they do not systematically aggregate for analysis communication streams.
Unified communications simplify compliance
Until now we recorded and stored the audio, messages, and video. Sometimes we ran speech to text so we could run keyword searches. When auditors asked, we pulled the tapes. But now, it seems that “record and store” is not enough.
To detect spoofing, firms are expanding their Enterprise Trading Risk Systems to aggregate, tag, and analyze messaging, video, and phone communications stemming from multiple siloed trading applications. Not just new modes of communications—but fragmented and multiple duplicative systems offering messaging, voice, and video connections—has made the job difficult.
However, a unified communications platform—as a core enterprise system—can give firms the tools, access points, and economies to efficiently feed multiple systems for surveillance, compliance, audit, and proprietary analysis.
Is Lexicon character matching effective communications surveillance?
In the Order, JPM attests to “update the universe of monitored employees and revise its lexicons on a regular basis to address evolving risks as well as utilize technology that allows for lexicon-based surveillance of voice recordings.”
Many experts believe lexicon character matching is not sufficient. More advanced electronic communications surveillance applies statistical methods to analyze networks, map relationships, and show interactions across groups of users.
Real-time unified communications surveillance: a new item for the Board agenda
Maybe, with the price of penalties and restitution going up, Compliance and Risk groups can prove an ROI to invest in a more rigorous communications surveillance system.
One thing is for sure, the CFTC’s notice to JPMorgan has just made the realm of real-time unified communications surveillance a billion-dollar topic for Board Rooms.
| Who pays? Respondents are liable for the acts of their agents | ||
| JPMorgan’s Billion-dollar spoofing case: the highest restitution ($311,737,008), disgorgement ($172,034,790), and civil monetary penalty ($436,431,811) amounts in any spoofing case. | ||
| JPMorgan Chase & Co | Bank Holding Company | Typical structure to separate regulatory licenses |
| JPMorgan Chase Bank, N.A. | Bank N.A. | A national banking association for consumer, commercial, and investment banking |
| J.P. Morgan Securities LLC | Securities LLC | Registered as a Futures Commission Merchant (“FCM”) and as a Swap Dealer with CFTC and an SEC-registered broker-dealer. |
Integrate RingCentral with key financial services industry tools, including Theta Lake, Smarsh, and Red Box. Or, build a custom integration with our open APIs. Go to App Gallery →
Updated Jul 01, 2025